2017 Resolutions

I came up with a few new years resolutions. In no particular order:
- write more (this website)
- use a journal
- organize my personal websites and their data. this is tricky, I have a few decades of web cruft.
- organize photos as they are taken
- spend a little time each day organizing my old photos. I also have a few decades of photos to organize.
- find creative ways to spend time with my kids that expand their minds and keep me youthful.
- go to bed earlier ; get up earlier. I'm a natural night-owl so this may be more of a short-lived experiment.
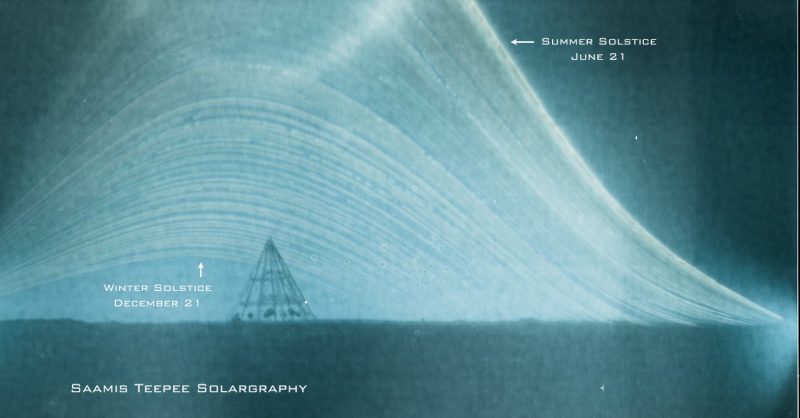
Happy Solstice!
The image below is an example of solargraphy. A pinhole camera is used to take a picture over 6 months. This photography technique perfectly illustrates the position of the sun between the summer and winter solstice.
Skylight Simulation
Trying to decide where to place some skylights in my garage renovation project, I needed to simluate the look. I took pictures of the one installed skylight from the perspective of the camera if it was installed in 2 places, and splicing them into a 'blank' image. Result:
 and
and

I decided to go with #2. Aside from the exposure and the skylight being open, very accurate!

Code & Pinot: UNIX!
I gave a presentation tonight at Nashville Girl Geek Dinner's Code & Pinot event. We went over some UNIX history and did a bit of command line intro. Action shot:
It was a great event! I had a lot of fun teaching something I'm passionate about (while de-rusting a bit on relating the basics!) and had some great conversation afterwards. I've given the history talk a number of times over the years, but the GGD Nashville crew got to experience my first test of this talk with slides! \o/ You can download my history presentation here. And here is the history of what I typed during the UNIX lesson.
Side note: We discussed the historically famous "Space Travel" game (look it up). But, all I knew was that it was a game...and I'm not a gamer. So, I had to look it up a bit more when I got home. Apparently it let you simulate travel between planets in our solar system and cost about $50-$75 in 1969 money to play a round on the GE 645 running MULTICS! Which is $320-$482 in 2015 money. No wonder re-writing the whole OS on cheaper hardware was worth it. :-P
If any of you were there and would like to know more, here are some good links that I used when re-acquainting myself with UNIX's colorful history and some beginner material:
More History of UNIX http://www.albion.com/security/intro-2.html http://web.mit.edu/saltzer/www/multics.html http://en.wikipedia.org/wiki/History_of_Unix http://en.wikipedia.org/wiki/Unix
Other Good Intros http://freeengineer.org/learnUNIXin10minutes.html http://cli.learncodethehardway.org/book/
Don’t have UNIX to play with? Get it in the browser with JS/UIX! http://www.masswerk.at/jsuix/
Cheat Sheets http://files.fosswire.com/2007/08/fwunixref.pdf http://sites.tufts.edu/cbi/files/2013/01/linux_cheat_sheet.pdf
Beers w/Trey
Trey came to town. So, we had beer. And I made picturefilms. Used a GoPro and the Radian, which had arrived a few days before. Still not great with it, but the results here were fun. Filmed at both Craft Brewed and M.L. Rose. Approximately 250X normal speed.
Thoughts on "negative-Kelvin"
Nature: Quantum gas goes below absolute zero.
I thought I had a decent understanding of physics. But after reading this, someone should revoke my 'amateur scientist' card. This (from Wikipedia) helped me understand it:
Since we started with over half the atoms in the spin-down state, initially this drives the system towards a 50/50 mixture, so the entropy is increasing, corresponding to a positive temperature. However, at some point more than half of the spins are in the spin-up position. In this case, adding additional energy reduces the entropy, since it moves the system further from a 50/50 mixture. This reduction in entropy with the addition of energy corresponds to a negative temperature.
This is not about the common notions of hot and cold, this is thermodynamic temperature, which is about entropy and energy. OK, so to me, this amounts to a neat physics trick. The universe will not collapse and our understanding of physics hasn't changed. Hopefully, it'll inspire a few folks (like me) to understand it better. Doing more reading, it reads like this only works in a 'system' of atoms, not with a singular atom. If you can't make a single atom colder than 0.0 kelvin, then the fundamental physics models don't change. Somewhat frustratingly, I see no mentions of anti-gravity, which was the most radical thing said on the nature.com article. So, please erase that and any anti-gravity belt predictions from your memory banks.
Speaking of theoretical maximums, another fascinating one is the concept of "absolute hot", which is currently defined as the Planck temperature, (1.416785×10^32^ kelvin). All physics models break down, even things like gravity. And, theory says that the entire universe has already experienced this temperature, a fraction of a second after the big bang. Enjoy that thought.
Further reading:
High-Speed Datacenter Work
Went to the datacenter last night to build out a few DB servers with 64GB of RAM. And set up a timelapse to record parts of the work. Marc, Brian and I did 2 servers each. You can see some up-close shots of the Dell R710 hardware, though it's quite blurry. Playback is 74 x normal speed.
Wasp Nest
Found a paper wasp nest today while we were having work done on the house. It was cold out and I thought they were dead...when I set it down in the sun to take a picture, I saw some movement. So, I filmed the little guy trying to get out. National Geographic here I come.
Rain Math
The storm headed our way tonight is predicted to drop 2" of rain over Nashville. If it covers the entire 527 square miles with that amount (on average), that storm would drop 152.8 billion pounds of water. Yay science.
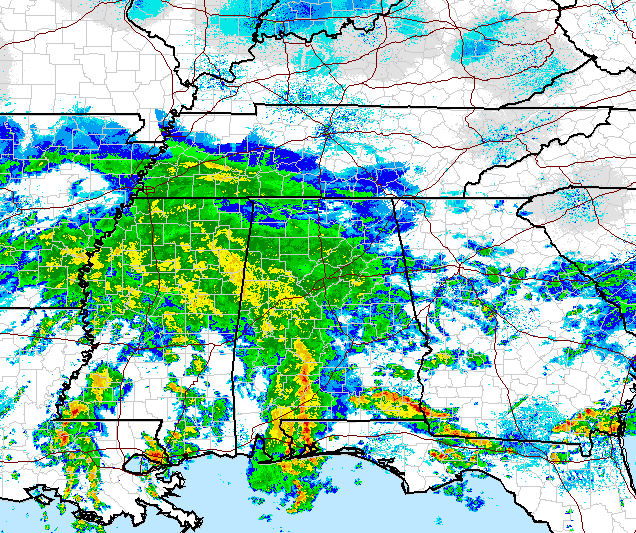
Here's my math:
1 inch of rain x 1 square mile = 65,785 cubic meters = 17,378,742 gallons
Nashville is 527 square miles according to Wikipedia.
A gallon of water weighs 8.35 lb.
So, 2 inches of rain over every inch of Nashville is 2 x 527 x 17,378,742 ....
Which is 18,317,194,068 gallons. Which weighs = 152,948,570,467 lb.
Yikes. I better go start mowing the yard like right now. I don't want to get killed when the rain falls on me
git + sudo + local ssh keys
Some colleagues and I wanted to be able to check out code onto a remote server using our local github ssh keys. And we should be able to do that as any user we please (for example, the deploy user). After a bit of research, I found that it's possible! In short, you use ssh-agent to pass your key credentials on to the remote server and set up sudo to pass those credentials along thru the environments. Let's do this!
I'm on a Mac, which has ssh-agent running by default. Yay! But, you still want to verify that your key is added to the agent:
laptop:~ n8foo$ ssh-add -l
2048 00:00:00:00:00:00:00:00:00:00:00:00:00:00:00:00
/Users/n8foo/.ssh/id_rsa (RSA)
Now, ssh into your remote server using the -A flag to ssh to pass auth along.
ssh -A remoteuser@remote.server.com
Test that ssh's agent auth worked:
[remoteuser@remote ~]$ ssh-add -l
2048 00:00:00:00:00:00:00:00:00:00:00:00:00:00:00:00
/Users/n8foo/.ssh/id_rsa (RSA)
Your keys should show up. Now, confirm that you can access github with your key from that remote server:
[remoteuser@remote ~]$ ssh -T git@github.com
Hi n8foo! You've successfully authenticated, but GitHub does not provide shell access.
OK, now let's enable this so we can switch users with sudo. Sudo needs to pass the SSH_AUTH_SOCK environment variable on through. To do that, add (or modify) the defaults line in /etc/sudoers to look something like this:
Defaults env_keep+=SSH_AUTH_SOCK
You can do this, if you have a default ubuntu sudo config:
# sed -i "s/^Defaults.*/Defaults env_keep+=SSH_AUTH_SOCK/g"
/etc/sudoers
Everything should be working now. Let's test...
[remoteuser@remote ~]$ sudo su - someotheruser
[someotheruser@remote ~]$ ssh -T git@github.com
Hi n8foo! You've successfully authenticated, but GitHub does not provide shell access.
You can now get your git on, directly on your remote machine, as another user. Done!
